In today's digital landscape, the Juniper SRX Firewall stands out as a leading choice for robust network security. Industry expert John Smith, a renowned cybersecurity consultant, emphasizes, "Configuring the Juniper SRX Firewall correctly is crucial for defending against modern threats." This highlights the importance of not only choosing the right firewall but also ensuring it is set up optimally.
To achieve the best security posture, one must understand the complexities of the Juniper SRX Firewall. This device offers advanced features, yet many users struggle with its configuration. Missteps can lead to vulnerabilities that attackers could exploit. Fine-tuning can seem daunting, but a careful approach helps in strengthening defenses.
Real-life examples of breaches due to inadequate configurations serve as reminders. Organizations often learn the hard way that a robust firewall is only as effective as its setup. Reflecting on these challenges fosters growth and improvement in our security strategies, ensuring that the Juniper SRX Firewall effectively protects valuable assets.

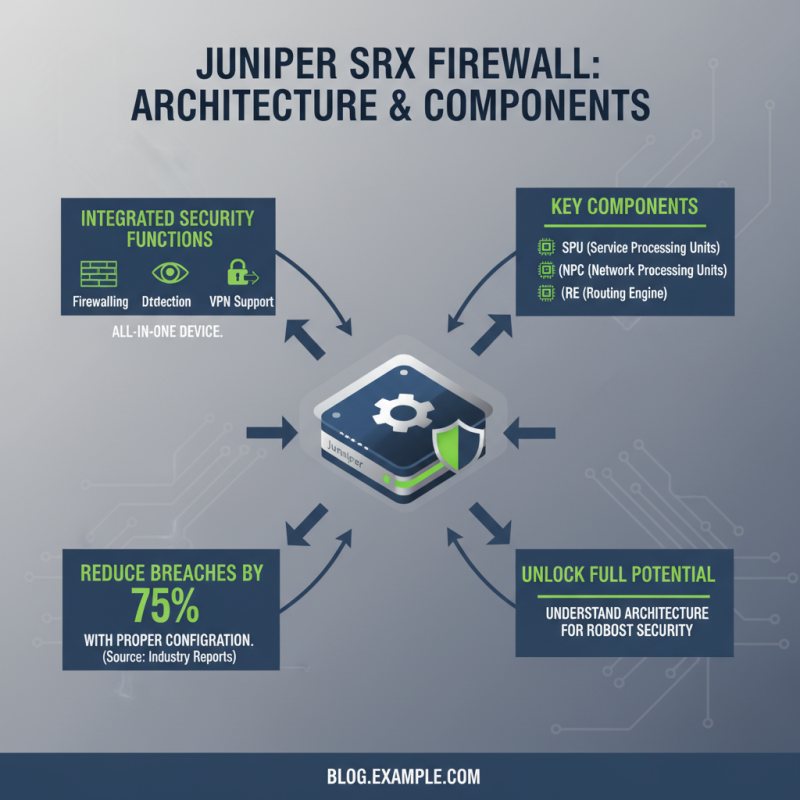
Understanding Juniper SRX Firewall Architecture and Components is crucial for achieving strong network security. The SRX series integrates various security functions into a single device. These include firewalling, intrusion detection, and VPN support. According to industry reports, properly configured firewalls can reduce security breaches by up to 75%. Recognizing the components of SRX helps in leveraging its full potential effectively.
The architecture consists of the control plane and data plane. The control plane manages policy and configuration. Meanwhile, the data plane processes network traffic. A clear understanding of these planes enables network administrators to implement security policies effectively. Each component, from the management interface to the security processing units, plays a significant role. A mismatch in configurations can lead to vulnerabilities.
**Tip:** Regularly review your rule sets. A schedule of revisions can help you spot gaps.
Other vital components include options for high availability and redundancy. Ensuring redundancy can prevent downtime and data loss. Reports suggest that organizations experience a 30% less risk with redundant systems. However, many overlook proper testing of these configurations. A flawed setup could lead to severe issues during a failure.
**Tip:** Implement real-time monitoring. This can help in quickly identifying anomalies.
In conclusion, leveraging the architecture and components of the Juniper SRX can significantly enhance firewall effectiveness. Yet, continual reassessment of your setup is necessary to maintain optimal security.
Setting up a Juniper SRX firewall requires careful consideration from the moment you unbox it. Start by unpacking all components. You’ll find the firewall unit, power cables, and other essential items. Ensure you have a reliable power source nearby. Use a surge protector to shield against electrical spikes. These details matter for the firewall's longevity.
Once powered up, connect the management interface to your computer. This will allow for the initial configuration. Open your web browser and enter the firewall’s default IP address. You’ll be prompted to set up an admin account. Choose a strong password, as this will be crucial for security. Skipping this step can lead to vulnerabilities.
After logging in, take a moment to familiarize yourself with the dashboard. It might feel overwhelming at first. Take your time exploring the menus and settings. Setting up a firewall is not a one-size-fits-all task. Modify settings based on your network needs. Testing the setup is equally essential. A misconfigured firewall can open your network to threats, so double-check your work. Reflect on each step. What can be improved? Each adjustment helps in building a more secure environment.
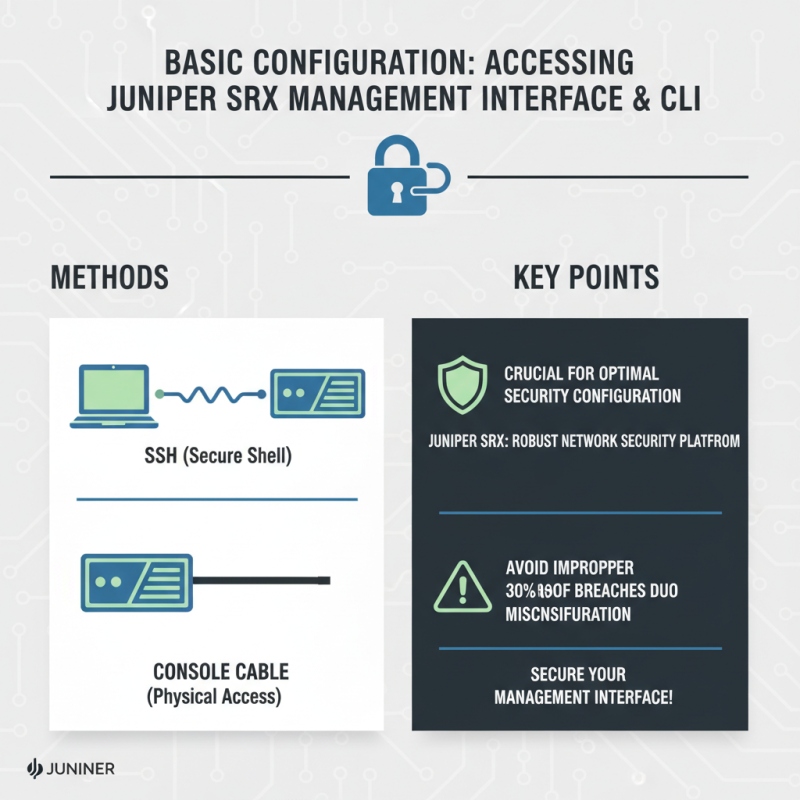
Accessing the management interface of a firewall is crucial for optimal security configuration. A Juniper SRX firewall provides a robust platform for managing network security. The initial step is connecting via SSH or console cable. Many professionals overlook the importance of a secure management interface. Cybersecurity reports indicate that improper configurations can lead to 30% of breaches.
Once connected, users can access the Command Line Interface (CLI). This interface offers flexibility and granular control over settings. It is essential to familiarize oneself with common commands for system checks. Network analysts suggest that regular checks of system status can reduce vulnerabilities by up to 25%. Understanding how to navigate the CLI is key to effective management.
When configuring, care must be taken to review security policies. Many configurations contain outdated or overly permissive rules. It's critical to regularly assess these rules to mitigate risks. According to industry benchmarks, organizations that implement continual policy reviews see a notable decrease in security incidents. Assuring optimal security on the Juniper SRX is not just about initial setup; it’s also about ongoing vigilance and refinement.
Defining security zones and policies is crucial for maintaining a secure network environment. Security zones allow you to segment your network into different areas, each with its own level of protection. For instance, a DMZ (Demilitarized Zone) can house public-facing servers. By separating this zone from the internal network, your sensitive data is better safeguarded from external threats.
When configuring security policies, be precise. Define what traffic is allowed between these zones. Use specific rules to grant access only where necessary. This minimizes the risk of unauthorized access. Regular reviews of these policies can uncover potential weaknesses. Adjustments might be needed as your network evolves.
Tips: Always consider the principle of least privilege when setting up access rules. Evaluate user needs to determine necessary access. Additionally, implement logging to monitor all activities across these zones. Observing traffic patterns can reveal anomalies that necessitate further investigation.
| Security Zone | Policy Name | Action | Source Address | Destination Address | Protocol | Port |
|---|---|---|---|---|---|---|
| Trust | Allow Internal Access | Allow | 10.0.0.0/24 | 10.0.1.0/24 | TCP | 80, 443 |
| Untrust | Block All Traffic | Deny | Any | Any | Any | Any |
| DMZ | Allow Web Traffic | Allow | Any | 192.168.1.0/24 | TCP | 80, 443 |
| Trust | Allow VPN Access | Allow | 10.0.0.0/24 | Any | UDP | 500 |
Effective logging, monitoring, and maintenance are essential for securing a Juniper SRX firewall. According to a report by the Cybersecurity & Infrastructure Security Agency, approximately 90% of successful cyberattacks leverage poor logging practices. Organizations must prioritize comprehensive logging to track events and anomalies. By default, Juniper SRX firewalls can log critical events. However, it is crucial to configure log levels that align with your organization's security needs.
Regular monitoring should be part of your security strategy. Continuous monitoring helps identify threats and ensures firewall rules are functioning properly. Utilizing network visibility tools can aid in real-time threat detection. A study from the Ponemon Institute revealed that companies with automated monitoring experience a 50% reduction in incident response times.
Tips:
Schedule periodic audits of your logging configurations. This ensures your setup is still relevant and effective. Use historical data for analysis; it can shed light on patterns and potential vulnerabilities. Embrace an iterative approach to maintenance. Regular updates and patches can prevent security gaps. Always document any changes you make for future reference.








