In today's digital landscape, configuring the Juniper SRX Firewall is crucial for optimal security. This powerful device offers various features to protect networks from threats. However, effective configuration is key to its success. Many users struggle to maximize its potential.
The Juniper SRX Firewall can serve as a robust line of defense. But improper settings can lead to vulnerabilities. Network administrators must pay attention to details. Security policies, monitoring tools, and regular updates are essential. However, common mistakes can hinder performance.
Understanding the unique features of the Juniper SRX Firewall allows for better decision-making. Each network is different, and a one-size-fits-all approach does not work. Reflecting on past configurations can reveal areas for improvement. Thus, the journey towards optimal security requires ongoing learning and adaptation.

Understanding the architecture of a security solution is crucial for effective cybersecurity. The structure of many firewalls prominently features a multi-layered approach. Each layer plays a specific role in threat detection and prevention. This system enhances security by ensuring that potential threats are analyzed at multiple points.
In a typical configuration, the first layer might focus on packet filtering. This involves examining packets and deciding whether they should be allowed or blocked. The subsequent layers often include stateful inspection. Here, the firewall tracks the state of active connections. This offers a deeper level of scrutiny and reinforces security measures.
However, it's essential to recognize that no system is foolproof. Certain configurations may lead to vulnerabilities. For instance, overly permissive traffic rules can create openings for attacks. Regularly reviewing and adjusting these settings is vital. Ongoing assessment ensures the firewall adapts to new threats effectively. Emphasizing the importance of understanding the underlying architecture will lead to more robust security practices.
This bar chart illustrates the optimization levels of various security configurations within the Juniper SRX Firewall as of 2026. Each category represents a critical aspect of security, where higher values indicate better optimization standards.
Configuring a firewall requires a solid foundation. Before diving into settings, ensure your environment is ready. Assess current network architecture to identify critical areas needing protection. Review device capabilities. Documentation is essential. Have data sheets on hand.
Consider these tips for clearer insights. Start with a logical layout. Document IP address schemas. Create a backup before making changes. This can save time if errors arise. Testing should happen incrementally. Mistakes are part of the process, but can often lead to better practices.
Always prioritize security policies. Ensure they align with organizational goals. Engage with team members. Collective input can shed light on overlooked vulnerabilities. Regularly review rules. Adapt them as threats evolve. Remember, security is an ongoing journey, not a one-time task.
| Dimension | Details |
|---|---|
| Firewall Model | SRX300 |
| Firmware Version | 20.4R1 |
| Initial Configuration Steps | Connect console cable and access CLI |
| Required Credentials | Default: admin/password |
| Network Interfaces | Ensure interfaces are configured for LAN and WAN |
| Security Policies | Define rules for inbound and outbound traffic |
| NAT Configuration | Set up NAT for internet access |
| Logging and Monitoring | Enable logging for security events |
| Backups | Regularly back up configuration settings |
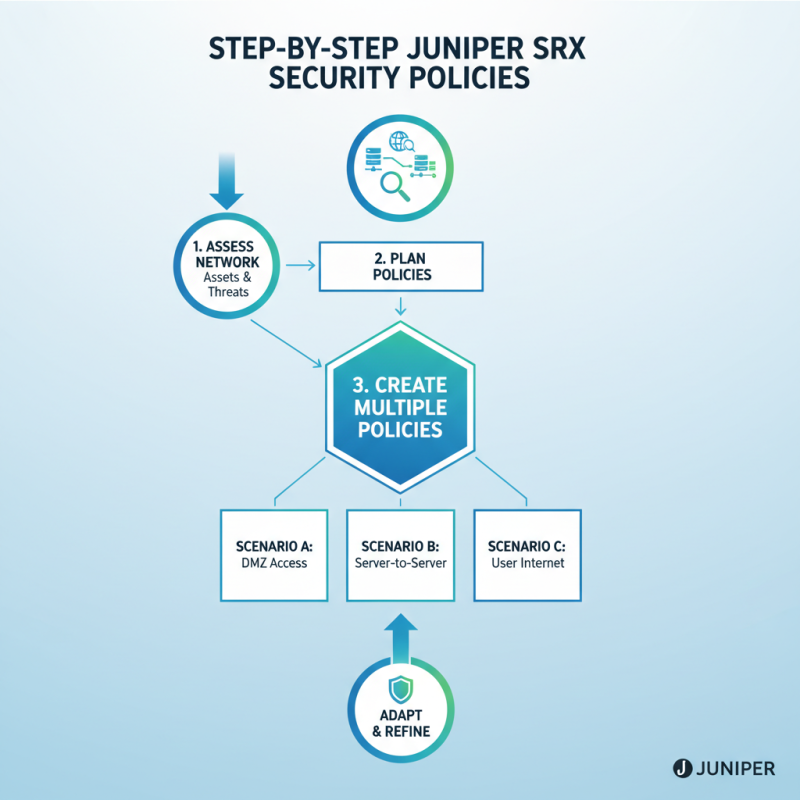
When configuring security policies on a firewall, clarity is key. The initial step is to assess your network environment. Identify critical assets and potential threats. This understanding will guide your policy creation. Create multiple policies for different scenarios. One size doesn’t fit all.
Next, focus on defining your rules. Start with basic traffic types. Allow essential services only. Deny everything else by default. This method minimizes vulnerabilities. Regularly review your policies. Are they too strict? What about user experience? Balance is vital.
Lastly, consider logging and monitoring. Implement comprehensive logging for all activities. It provides insight into potential breaches. However, this can lead to data overload. You may miss key alerts among the noise. Periodic assessments of your logs are essential. Reflect on your configuration. Always strive for improvement.

Implementing a VPN on firewalls provides secure connections for remote users. According to industry reports, 30% of companies now prioritize VPNs as remote work increases. Many fail to configure VPNs properly, exposing risks. Ensure that strong encryption protocols are used. Lack of this can lead to data breaches.
Intrusion Prevention Systems (IPS) play a critical role in firewall security. A study by Cybersecurity Ventures indicates that cybercrime will cost the world $6 trillion annually by 2021. This number continues to rise. An effective IPS reduces this risk by identifying and blocking potential threats in real-time. Regular updates and tuning of IPS settings are essential but often neglected. Failure to adapt can lead to vulnerabilities.
Monitoring traffic and logs helps in fine-tuning both VPN and IPS. Most organizations overlook this. Continuous analysis can reveal unusual patterns. Over time, attackers evolve tactics. Thus, ongoing vigilance is necessary to maintain optimal security. Regularly review and adjust configurations based on threat landscape changes.
Regular monitoring and maintenance are crucial for ensuring the security of your firewall. A dynamic threat landscape means risks are constantly evolving. You cannot simply deploy a firewall and forget about it. Log files should be regularly reviewed to detect suspicious activities. Timely updates help protect against newly discovered vulnerabilities.
Routine maintenance includes testing configurations. Misconfigurations can create openings for attackers. Analyze traffic patterns to identify anomalies. This process helps fine-tune firewall rules. It’s essential to adapt to changing network environments and user behaviors. Over time, policies that once worked may no longer be effective.
Establish a consistent review schedule. Monthly checks can catch issues early. Yet, don’t overlook the value of community feedback. Engaging with peers can reveal blind spots in your security posture. Challenge your assumptions regularly. Remember, complacency can lead to unforeseen risks. Regular engagement is key to staying ahead in security.








